If you use a computer to access the internet, chances are high you are familiar with malicious software. Malicious software, commonly referred to as “malware,” is software designed to gain unauthorized access to or deliberately cause damage to a computer.
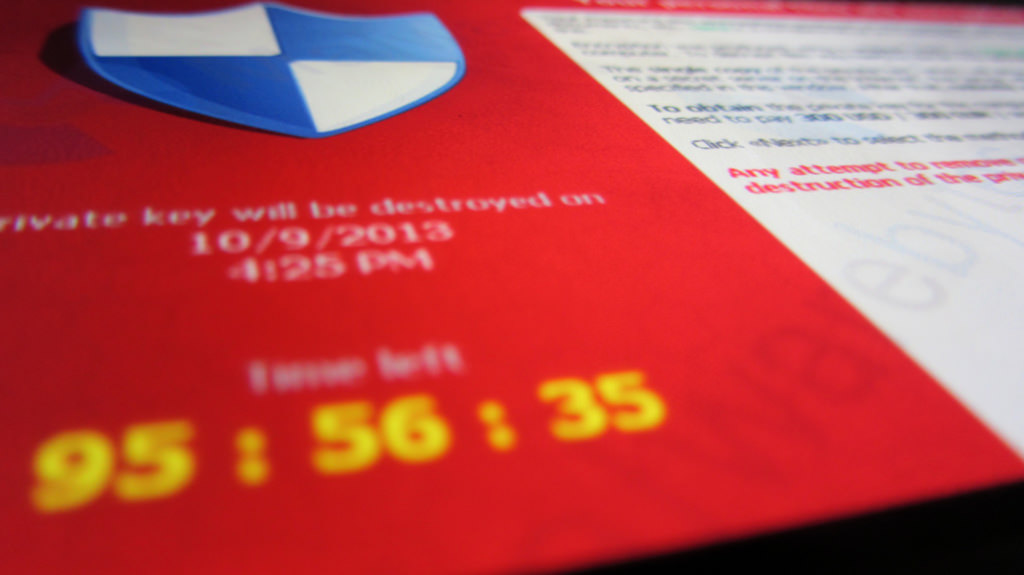
The impact of malware to the user can range from annoyances like pop up advertisements and slowed PC performance to more serious consequences like theft of confidential data and personal information. This year the biggest malware threat impacting businesses is ransomware: a form of malware that allows a hacker to access and encrypt a user’s computer, essentially holding the PC and its content “hostage,” so that the hacker can demand payment (or ransom) to decrypt it and restore access to the owner.
How Does Ransomware Get On My PC?
It is important to understand how ransomware and other forms of malware gain access to your PC if you are to prevent it.
Most ransomware is distributed through email as an attachment. Cyber criminals have become very sophisticated in the creation and delivery of malicious emails. These fraudulent pieces of email are made to look like an important piece of information from a legitimate sender. They commonly look like a message from a courier like FedEx or UPS that encourages the recipient to open an attachment containing delivery tracking information. Another common email tactic is a generic introduction from a miscellaneous company with a message referring to an invoice that is attached for payment. The malware is contained in the attachment referenced in those emails. Should a recipient open the attachment, the malware is installed on the PC often unbeknownst to the PC owner.
Be diligent with your email. Do not open email attachments from unknown senders. When in doubt, throw it out.
Websites
Another common way that ransomware makes its way to your PC is through “drive by downloads” from shady websites. A drive-by-download attack does not require a user to click on an attachment as with email delivery techniques. These attacks are the result of a sophisticated hacker who is able to embed hidden code into a malicious website. The code executes the download of ransomware to the user’s PC when the user merely visits the website containing the virus.
To avoid this type of attack, inspect website addresses thoroughly. Never click on a web link sent to you by email from an unknown sender (or, for that matter, from a known sender if the website address looks suspicious or the email is in any way unusual).
Pirated Software
It should go without saying that you should never, ever install software that you do not obtain through legitimate means. When you use pirated software you are not only breaking the law and infringing on the copyright of the software manufacturer, but you are also putting yourself at serious risk of downloading ransomware.
Additional Ways to Avoid Ransomware
In addition to remaining vigilant with your email and internet surfing activities, there are a number of steps you can take to decrease your likelihood of being the victim of ransomware.
- Secure Your Network.
Set up firewalls. Secure your wireless network. Be aware of what ports are open on your network and close any that are unnecessarily open. Think about your wifi enabled devices and ensure they have strong passwords in use to secure them. Consider the use of web filters to control what websites can be accessed by users on your network. Proactively monitor your network for activities that should not be taking place in your environment. Doing all of these things will reduce the level of risk in your network environment.
- Limit user privileges.
Do not provide administrator level privileges to user accounts for everyday use. While it can be an annoyance for users to have to request administrative level assistance when they are performing legitimate updates to their PC, limiting this access provides a second layer of protection from ransomware. This is because malware often requires full access to your PC to run properly.When you are not operating your PC with administrative privileges, you will be notified if any software or application tries to make any changes to your system thereby alerting you to a problem before it occurs.
- Install antivirus software and keep it up to date.
- Keep your software and operating system up to date.
An additional way hackers distribute malicious software is through known vulnerabilities in popular software packages and operating systems. Software manufacturers regularly release updates to software to patch security holes in their software as they are discovered. Apply the updates immediately to close known gaps in security.
- Backup regularly.
You know the importance of backing up your data. This is yet another reason to be diligent with the practice. Should you become a victim of ransomware, you’ll still have access to important documents.
Should You Pay the Ransom?
Following these tips will significantly reduce the likelihood that you will be a victim of ransomware. What if, despite your best effort, you do become a victim of ransomware? Should you pay the ransom to regain access to your files? Law enforcement and security experts say no, not unless you absolutely have to. In fact, there is no guarantee, even with payment, you will regain access to your files. Don’t put yourself in a position to have to make that decision. Diligently protect, secure, and backup your systems regularly.